Make life easier with Application Filters
- Reaper

- Nov 14, 2020
- 3 min read
One of the harder tasks while maintaining a structured security rulebase, is determining which applications should or should not be allowed.
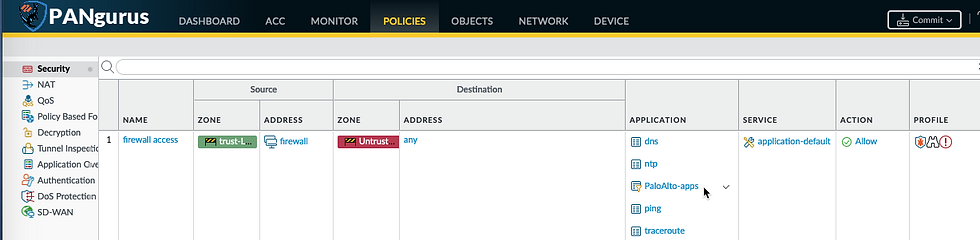
The list of applications can grow quite large depending on the needs of the business and users, and to make things worse: many common applications have several sub-applications, as you can see from the example below, which could introduce more difficulties as some may need to be blocked or allowed individually

To top this all off, regular content updates introduce new applications and sub-applications all the time. This allows for more granularity in controlling which applications are allowed or denied, but this can become an arduous task to maintain if applications are added to security rules manually.
An extremely versatile and often overlooked tool in the admin's arsenal is the Application Filter. The Application Filters can be found in the Objects tab just below the Applications and is used to dynamically build an Application Group, based on Application attributes and characteristics, rather than specific applications.

Next to each attribute the number of (currently) matching applications is listed. Selecting multiple attributes from the same column will act as an OR filter, selecting more attributes from other columns will act as an AND filter. The resulting applications that match the filter are listed at the bottom.
One of the first Application Filter everyone should create, is the Palo Alto services app based on the Palo Alto Networks tag, as shown below. The advantage to using this tag in an Application Filter is that any new services or applications added by Palo Alto Networks will automatically be added in the Application Filter, and thus the security rule where this App Filter is used in.

The Application Filter can then be added to a security policy just like a regular application as
Now we can start creating more Application Filters to block out undesirable applications by negative attributes, or allow them based on acceptable attributes.
As illustrated below; when we select the file-sharing Subcategory, the Categories that do not contain applications that match this Subcategory are removed from view. We can click additional sub-categories to include in this filter, or select more attributes like the risk factor, tags, or characteristics. for each option selected, the applications are updated. If any applications are included in the filter that do match the desired attributes, but you do not want to have included in the filter, they can be removed by clicking the Exclude box to the right of the application.

The applications that can be allowed by any organization will depend on many factors, so each deployment will have it's own unique requirements. A good strategy is to allow for a broad selection of benign applications, and blocking malignant or undesirable applications through filters in a different security policy placed higher in the rulebase.
Below is a good baseline for commonly used applications, building a selection of allowed applications could require building several, more specific, Application Filters rather than fitting everything into a single filter.

If you're wondering how to create application filters from CLI, these are the set commands to be used in configure mode:
set application-filter "good applications" category [ business-systems collaboration general-internet networking ]
set application-filter "good applications" subcategory [ encrypted-tunnel general-business instant-messaging internet-conferencing internet-utility office-programs social-business social-networking software-update ]
set application-filter "good applications" technology [ browser-based client-server ]
set application-filter "good applications" risk [ 1 2 3 4 ]
set application-filter "good applications" pervasive yesAny new applications downloaded through the monthly content update will be added to the Application Filters automatically.
Please feel free to leave a comment or ask questions below.
Reaper out


Comments